Firewallrule
From Wiki of WFilter NG Firewall
(Difference between revisions)
(→Advanced Settings) |
|||
| Line 12: | Line 12: | ||
** "Inbound", packet targets to the NGF device. | ** "Inbound", packet targets to the NGF device. | ||
** "Forward", packet being forwarded. | ** "Forward", packet being forwarded. | ||
| − | * '''Source IP''': packet source ip address. You can define IP as "Any", "Single" | + | * '''Source IP''': packet source ip address. You can define IP as "Any", "Single", "Range" and "Customize". |
** For "Single", a single ip or subnet is allowed(for example: 192.168.1.10 or 192.168.1.0/24). | ** For "Single", a single ip or subnet is allowed(for example: 192.168.1.10 or 192.168.1.0/24). | ||
** For "Range", you need to input an ip range. | ** For "Range", you need to input an ip range. | ||
| Line 30: | Line 30: | ||
* You may use '''time''', '''from-to''' and '''effective on''' to define a time period for this rule to be applied. | * You may use '''time''', '''from-to''' and '''effective on''' to define a time period for this rule to be applied. | ||
| − | == Customize | + | == Customize IP == |
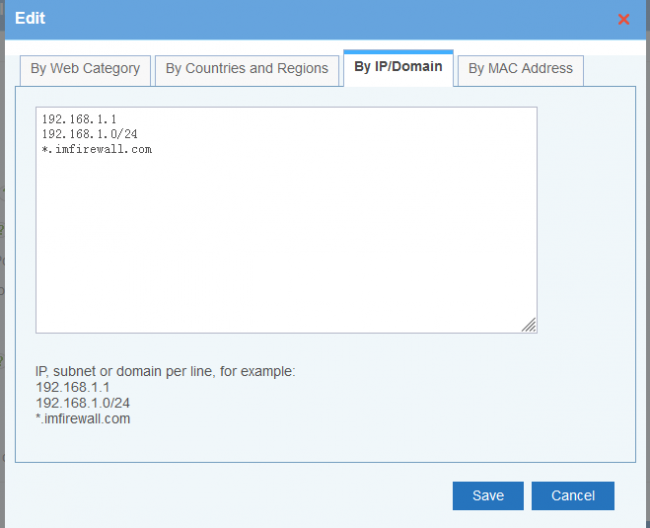
| − | Upon "Customize", you can block ip, subnets, domains and domain categories. For domains, WFilter will add dns replied ip addresses into the deny/allow list. | + | Upon "Customize", you can block ip, subnets, countries and regions, domains and domain categories. For domains, WFilter will add dns replied ip addresses into the deny/allow list. |
[[File: ros_firewall_dstip01.png|650px]] | [[File: ros_firewall_dstip01.png|650px]] | ||
| Line 39: | Line 39: | ||
[[File: ros_firewall_dstip03.png|650px]] | [[File: ros_firewall_dstip03.png|650px]] | ||
| + | |||
| + | [[File: ros_firewall_dstip04.png|650px]] | ||
IP, subnet or domain per line, for example: | IP, subnet or domain per line, for example: | ||
Revision as of 12:27, 12 November 2019
"Firewall Rules" block or allow traffic based on IP and ports. If you need "URL filter", "application control" and so on, you need to check modules in "Access Policy".
Contents |
1 New Rule
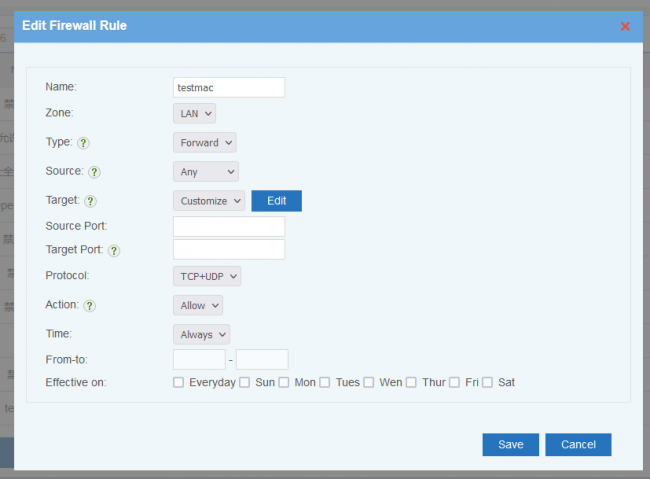
New a firewall rule, descriptions:
- Interface: "LAN" or "WAN". WAN interface is invalid in bridge mode.
- Type: packet direction.
- "Inbound", packet targets to the NGF device.
- "Forward", packet being forwarded.
- Source IP: packet source ip address. You can define IP as "Any", "Single", "Range" and "Customize".
- For "Single", a single ip or subnet is allowed(for example: 192.168.1.10 or 192.168.1.0/24).
- For "Range", you need to input an ip range.
- Target IP: packet target ip address, can be "Any", "Single", "Range" and "Customize".
- Target Port: packet target port, can be a single port or a port range, Syntax:
- One port: 8000
- A port range: 8000:9000
- Multiple ports: 80 8000
- Port and ranges: 80 8000:9000
- Protocol
- All: means all protocols, including TCP, UDP, ICMP and other IP protocols.
- TCP+UDP: both TCP and UDP.
- Action:
- "Reject": the rejected clients will get a RST packet immediately.
- "Drop": packets will be dropped, the clients will wait for connection timeout.
- "Allow": allow packet
- You may use time, from-to and effective on to define a time period for this rule to be applied.
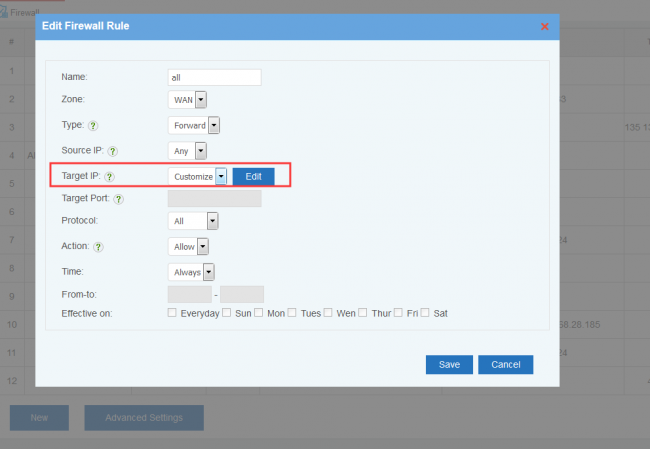
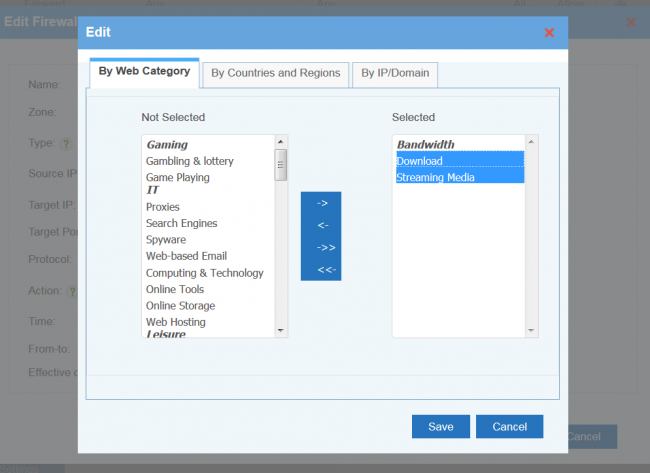
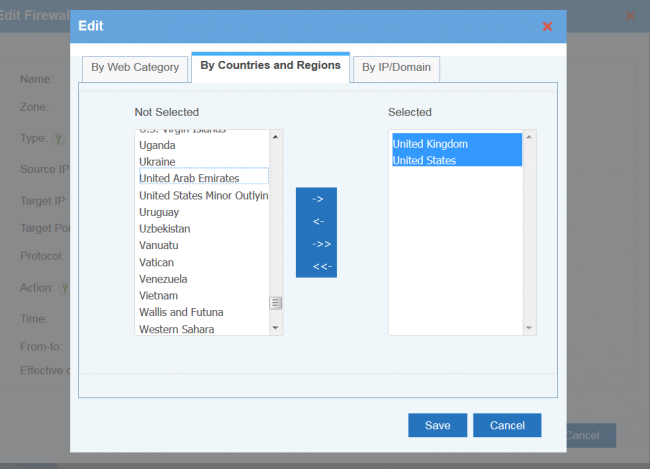
2 Customize IP
Upon "Customize", you can block ip, subnets, countries and regions, domains and domain categories. For domains, WFilter will add dns replied ip addresses into the deny/allow list.
IP, subnet or domain per line, for example:
192.168.1.1
192.168.1.0/24
- .imfirewall.com
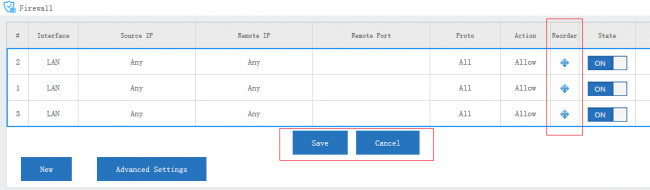
3 Processing Order for Rules
Rules are always processed from the top of a list down, first match wins. Understanding this order is especially important. You may drag the re-order icon to re-order rules.
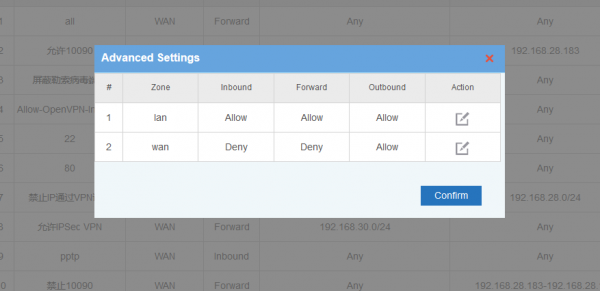
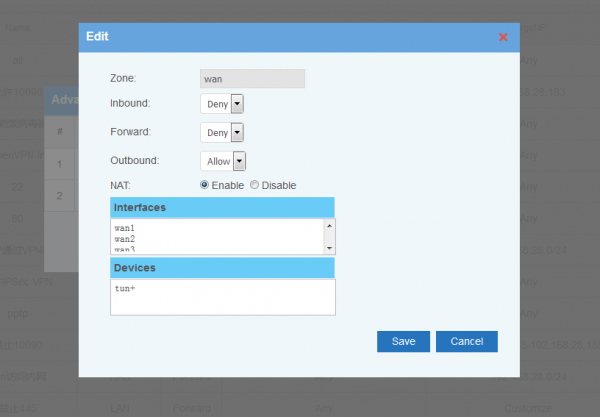
4 Advanced Settings
In "Advanced Settings", you can setup default policies for ZONEs. Two Zones(LAN and WAN) are supported in default.