Ipsecvpn
(→Tunnel Status) |
(→IPSec Tunnel Settings) |
||
| Line 25: | Line 25: | ||
* PreShared Key: tunnel secret key. With a correct key, the tunnel can not be established. | * PreShared Key: tunnel secret key. With a correct key, the tunnel can not be established. | ||
* Start: Manually or Automatically. | * Start: Manually or Automatically. | ||
| − | * IKE, ESP: algorithm for authentication and transfer. Both sides of the tunnel shall have the same algorithm. | + | * IKE, ESP: algorithm for authentication and transfer. Both sides of the tunnel shall have the same version and algorithm. |
Server side settings examples: | Server side settings examples: | ||
Revision as of 17:15, 26 October 2018
Contents |
1 IPSec Tunnels
This modules can build IPSec tunnels between multiple WFilter NGF networks, and make a secure site-to-site VPN. The number of IPSec Tunnels depends on your hardware performance, there is no software limit on the tunnels number.
2 IPSec Tunnel Settings
Before you setup a IPSec tunnel, you need to design your tunnels. For example:
- Suppose you have 3 network: A, B, C.
- A has a static public IP, B and C ip addresses are dynamic.
The solution will be:
- A, B, C shall have differenct subnets. For example: 192.168.10.x, 192.168.20.x, 172.16.1.x.
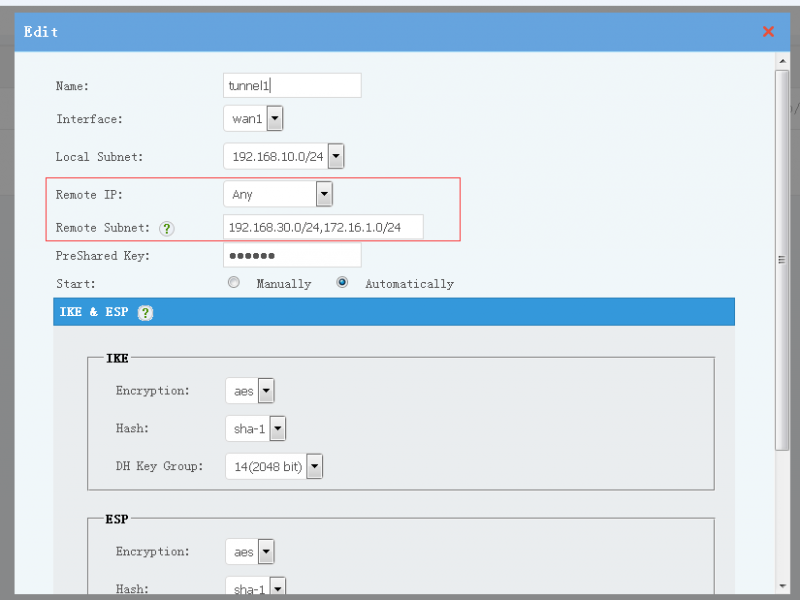
- Create a tunnel in A network, set "Remote IP" to "Any".
- Create tunnels in B and C networks, set "Remote IP" to A's public ip address.
- Now the tunnels are ready. A, B, C now are in a VPN network. The tunnels are between AB and AC.
- To enable access between B and C, you need to setup routering rules and enable FORWARD in A.
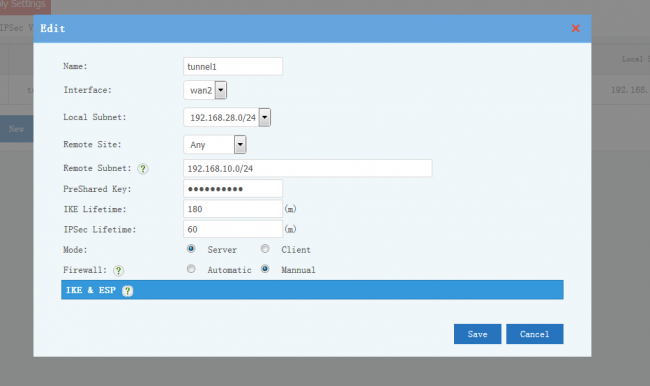
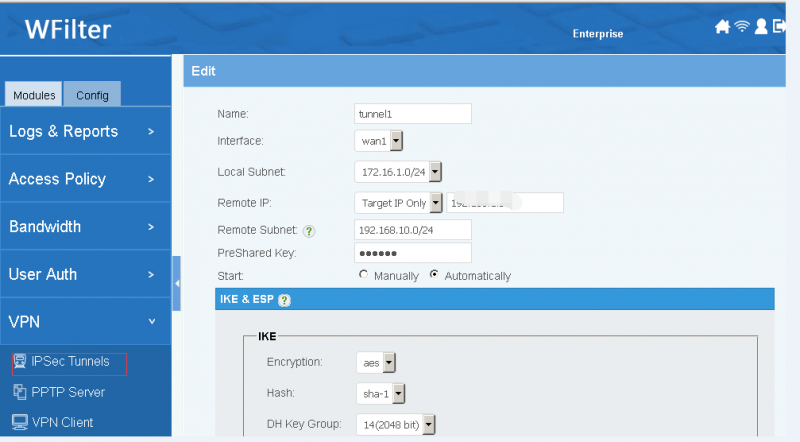
Description of tunnel settings:
- Name: tunnel name.
- Interface: WAN interface to setup the tunnel.
- Local Subnet: local subnet to be connected with the tunnel.
- Remote Site: another side of the tunnel, "Any" to allow any others to connect. The remote site can be an IP address or domain.
- Remote Subnet: remote LAN subnets which will be forwarded to the tunnel.
- PreShared Key: tunnel secret key. With a correct key, the tunnel can not be established.
- Start: Manually or Automatically.
- IKE, ESP: algorithm for authentication and transfer. Both sides of the tunnel shall have the same version and algorithm.
Server side settings examples:
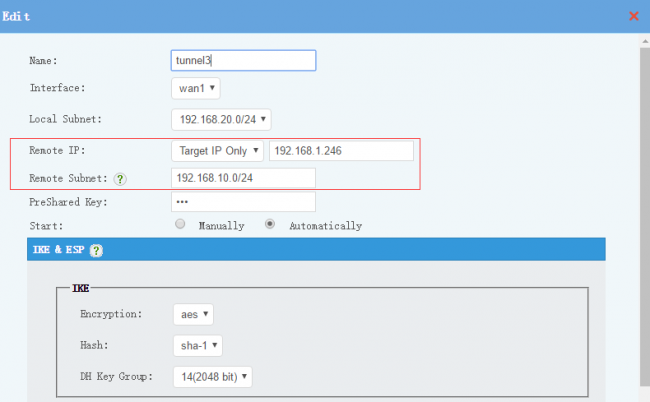
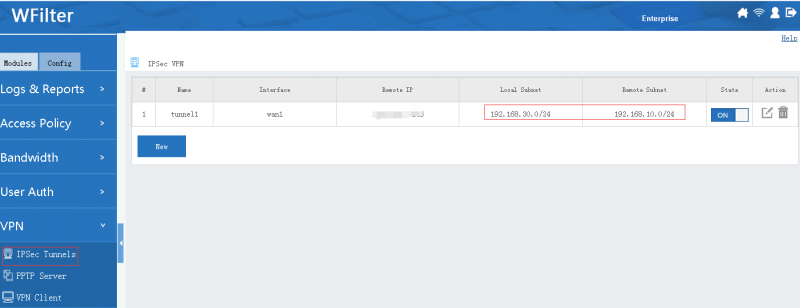
Client side settings examples:
Notice:
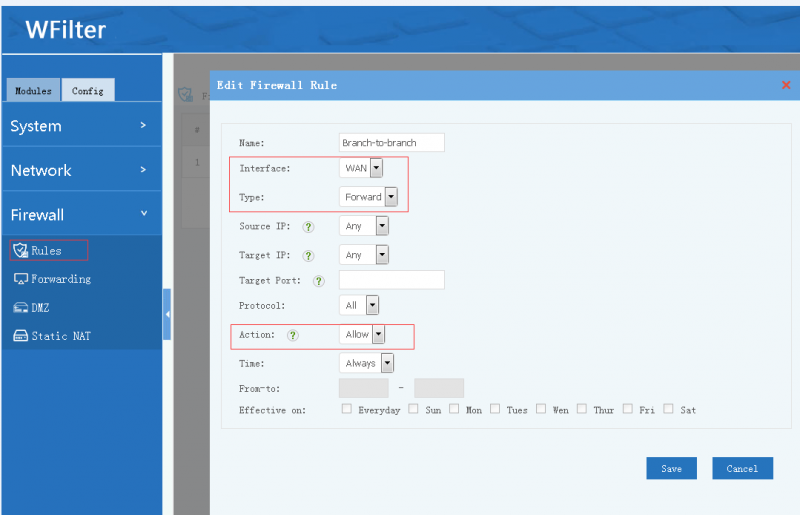
- Access of tunnels are also applied with firewall rules. For example, if you want to block VPN tunnels users from accessing a local server, you need to setup a firewall rule to block the target server ip from WAN interface.
- If you enable DMZ or "Static NAT", please add IPSec port "500,4500" to "port exception". Otherwise, IPSec connections can not be established.
- If the WAN interface has multiple static ip addresses, IPSec only listens in the first IP address.
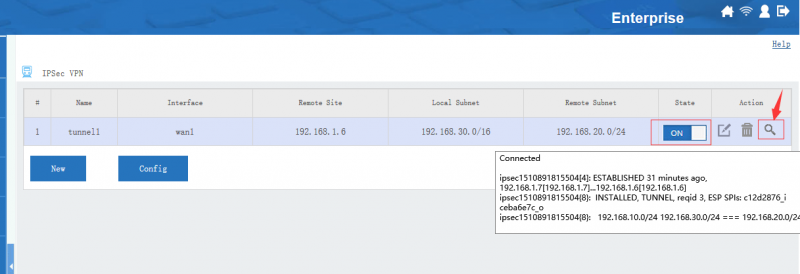
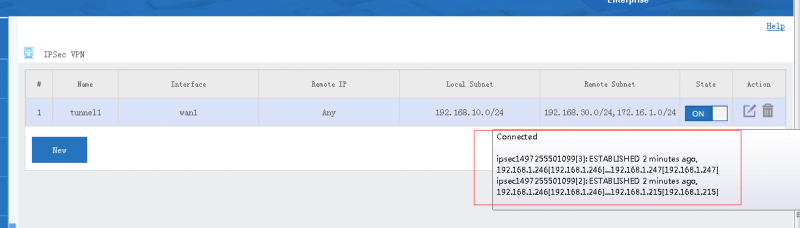
3 Tunnel Status
Move your mouse into the "state" icon, you will see the tunnel status and connected clients. You also can click the "view log" icon to check more log details.
4 A site to site ipsec vpn sample
Suppose you have 3 networks:
- Headquarter A, static public ip address, LAN subnet is 192.168.10.0/24.
- Branch B, PPPoE internet access, LAN subnet is 192.168.30.0/24.
- Branch C, PPPoE internet access, LAN subnet is 172.16.1.0/24.
Now let me guide you to build a virtual private network(VPN) for these three locations.
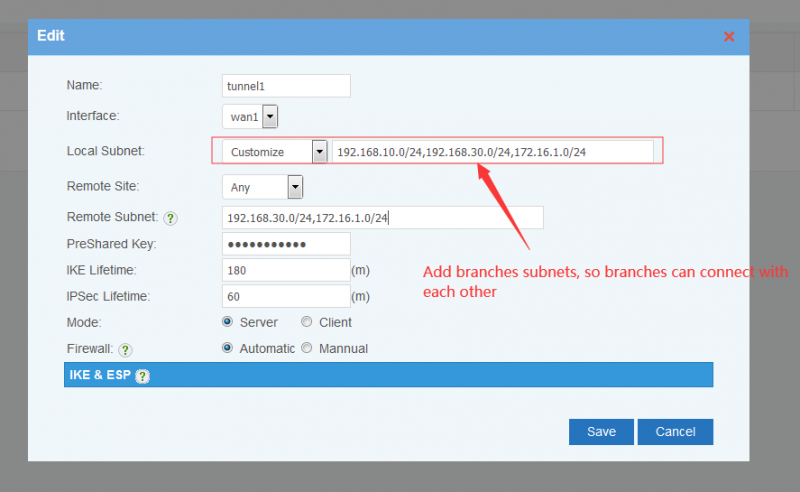
4.1 Settings for Headquarter A
- Setup the IPSec tunnel
- Enable forwarding of branches
Without this setting, branches can access headquarter, but no access between branches.
4.2 Branch B
- Setup the IPSec tunnel
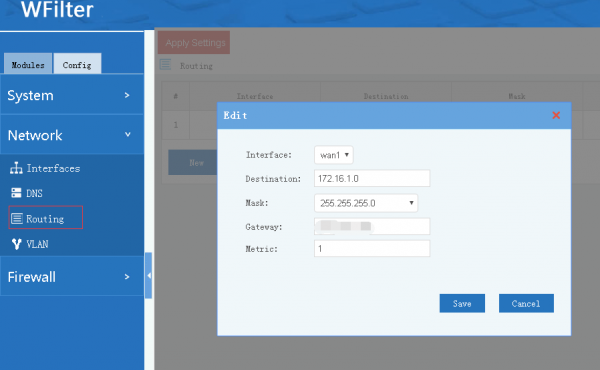
- Add a routing rule to branch C
Set branch C's LAN subnet to "Destination", set headquarter A's public IP to "Gateway". Without this routing rule, branch B can not access branch C.
4.3 Branch C
- Setup the IPSec tunnel
- Add a routing rule to branch B
Set branch B's LAN subnet to "Destination", set headquarter A's public IP to "Gateway". Without this routing rule, branch C can not access branch B.
By above steps, A,B,C are now in a virtual private network. If you don't want access between B and C, there is no need to add the firewall and routing rules.
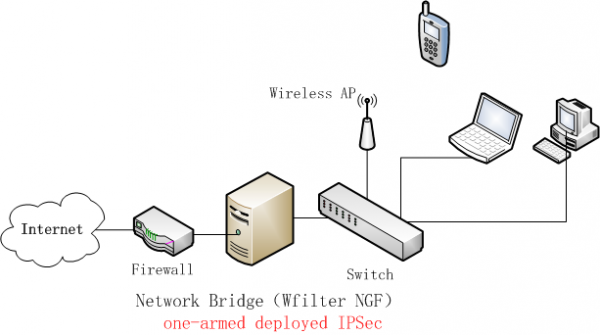
5 One-armed Deployment of IPSecVPN
As below network diagram, WFilter NGF is deployed as a network bridge. For IPSec VPN, this is called "one-armed deployment".
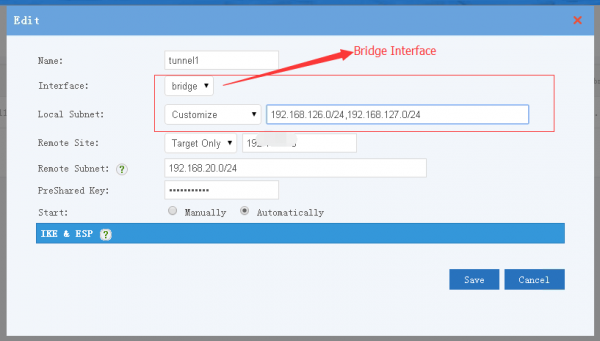
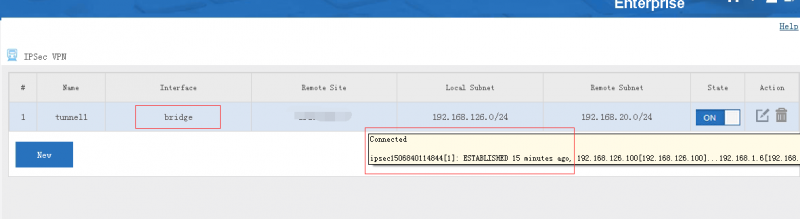
5.1 Setup the IPSec tunnel
Choose "bridge" as the interface, you might need to setup customize local subnets.
5.2 Setup port forwarding in gateway
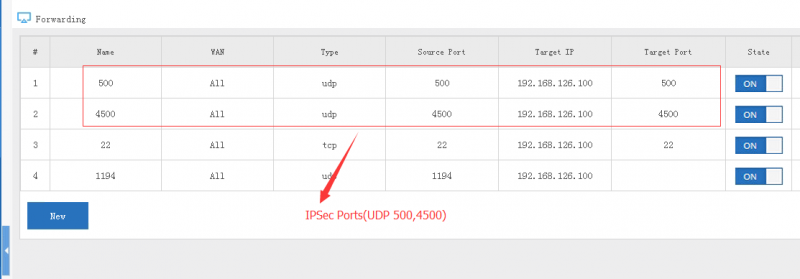
Gateway device needs to map the IPSec ports(UDP 500 and UDP 4500) to WFilter NGF.
5.3 Setup routing in gateway
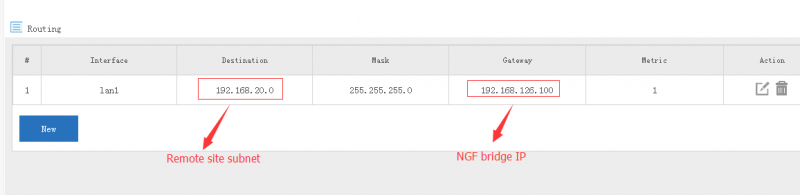
You also need to setup static routing in gateway to point nexthop of remote subnet to WFilter NGF.
IPSec tunnels are available now.